Logs are records of activities also generated by systems, applications, and network devices. They store information about the behavior of the systems, including accesses, errors, transactions, among other events. Log analysis is a fundamental technique in information security in general, enabling the monitoring of system behavior and identification of potential threats.
The lack of proper logging and monitoring can have severe consequences in the event of an attack on an application. In this article, we’ll discuss the negative impacts of poor logging and monitoring when there is an attack, the challenges faced by security teams, and the importance of implementing effective logging and monitoring practices to protect applications.
Read also: Writing Secure Code – A Best Practices Guide
Lack of log recording
When an application is the target of an attack, the lack of detailed logs can make it challenging to identify the source and the techniques used by attackers.
Without a clear record of activities, it’s difficult to track and understand how the attack occurred, what vulnerabilities were exploited, and what data might have been compromised. This lack of visibility can result in a slow and ineffective response to the incident, allowing attackers to do more damage and maintain unauthorized access to the application.
Furthermore, the lack of continuous monitoring prevents early detection of suspicious activity or abnormal behavior. This can result in a delay in incident identification, allowing attackers time to exploit application vulnerabilities and further compromise data and infrastructure.
The lack of proper logs and monitoring also makes post-attack investigation and identification of application security weaknesses difficult.
Without detailed records of activities during the attack, the security team will struggle to fully understand the incident’s impact, identify exploited vulnerabilities, and implement effective remedial measures. This could result in an ongoing vulnerability in the application, leaving it open to future attacks.
To overcome these challenges, it is crucial to implement effective logging and monitoring practices. This includes defining clear logging policies that cover information relevant to application security, such as authentication events, user actions, and system activities. In addition, the security team should establish an ongoing monitoring system that immediately alerts them to suspicious activity or abnormal behavior.
Tools and documentation in Logs and Monitoring
Logging and monitoring tools can also be used to simplify and automate the process. Implementing SIEM (Security Information and Event Management) tools is essential for application security, as it collects and analyzes security events in real-time from various sources, such as system logs and network devices. With advanced correlation and analysis capabilities, it identifies suspicious activity, detects threats, and generates alerts to the security team.
In addition, these tools can generate specific reports that help organizations demonstrate compliance with standards such as PCI-DSS, HIPAA, LGPD, and GDPR. They also enable retrospective investigations and help with regulatory compliance, strengthening organizations’ ability to detect, respond to, and protect their applications from cyberattacks.
In the context of web applications, log analysis is especially important for identifying vulnerabilities and attacks on web applications. Information security solutions, such as OWASP ZAP and Burp Suite, include advanced log analysis capabilities to identify potential vulnerabilities in web applications.
The importance of proper logging is also widely recognized in the AppSec space. Several resources and guidelines, such as the OWASP “Logging Cheat Sheet” and the “OWASP Logging Guide” highlight the need to implement effective logging practices.
OWASP’s “Logging Cheat Sheet” indicates that security event logs can provide crucial information about intrusion attempts, malicious behavior, and vulnerability exploitation. The “OWASP Logging Guide” highlights that proper logging can help recreate events and identify the root causes of security incidents, allowing for an effective response.
In a security breach, well-structured logs are essential for forensic analysis. They can help reconstruct the sequence of events, identify the scope of the incident, and support subsequent legal action. Therefore, combining the use of SIEM tools with the implementation of proper logging practices significantly strengthens the security posture of organizations.
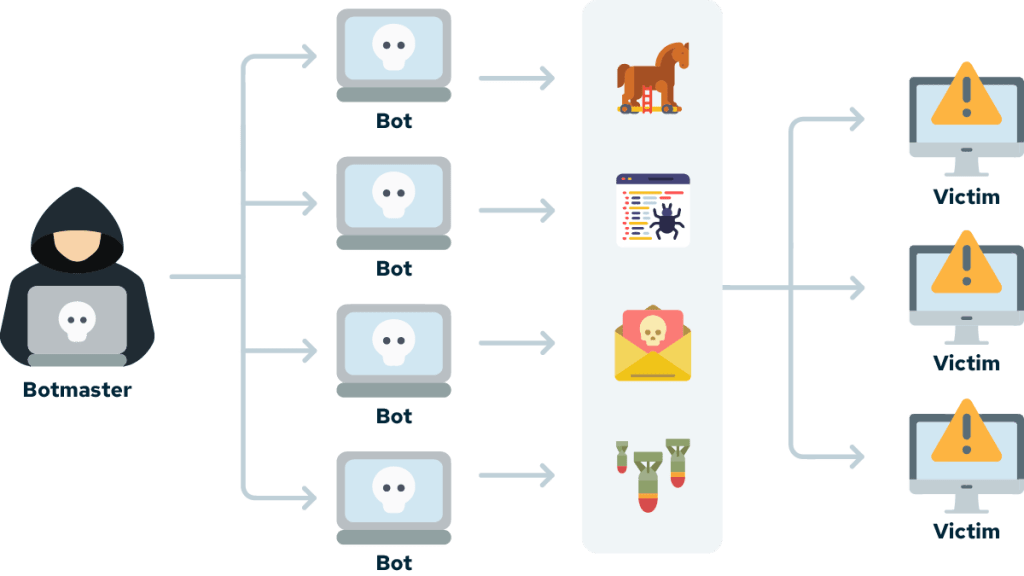
In the figure below, we see an example of Monitoring and log:

Negative impacts on a web application – Hypothetical scenario
Suppose an e-commerce web application is facing a series of brute-force attacks against user accounts. Attackers are trying to gain unauthorized access to accounts using combinations of common usernames and passwords.
However, due to the lack of proper logs, the security team is not aware of these attacks in real-time. There are no detailed logs of failed login attempts, attackers’ IP addresses, or any other indicators of suspicious activity.
Without proper logs, the security team is unable to identify the ongoing attack pattern or quantify the extent of the problem. They don’t have information about the specific user accounts being targeted or the passwords attackers are trying to use.
Consequently, the security team cannot take immediate action to mitigate the attack. They are unable to block attackers’ IP addresses, impose additional restrictions on login attempts, or notify affected users of suspicious activity on their accounts.
As a result, attackers continue to carry out successful attacks, gaining access to user accounts and compromising personal information such as payment details and purchase history. Users can suffer financial losses and have their confidence in the application shaken.
If proper logging was in place, security staff would be immediately alerted to failed login attempts and would have visibility into relevant details such as attackers’ IP addresses. This would allow for a quick and effective response, such as blocking suspicious IP addresses and enforcing additional security measures to protect user accounts.
Identifying and mitigating the vulnerability
One of the critical vulnerabilities identified by the OWASP Top 10 of 2021 is A09:2021-Security Logging and Monitoring Failures. This vulnerability highlights the importance of properly configuring the logging and monitoring systems to capture relevant security events.
To mitigate this vulnerability, it is recommended to follow the OWASP Application Security Verification Standard (ASVS) guidelines, which provide a set of controls and requirements for building secure applications. The ASVS, in its Level 2 and 3 requirements, highlights the importance of implementing adequate logging and security monitoring to identify and respond to security incidents.
In addition, it is critical to be aware of known vulnerabilities and their corresponding Common Vulnerabilities and Exposures (CVE). Several CVEs related to security monitoring and logging flaws have been identified and fixed in different software and systems. Keeping up-to-date on relevant CVEs and applying security patches and updates is an essential practice to strengthen the security posture of applications and prevent exploitation of these vulnerabilities.
Conclusion about Logs and Monitoring
In conclusion, the lack of proper logging and monitoring during an application attack can lead to severe consequences. The absence of detailed records makes it difficult to identify the source of the attack and take effective measures to protect the application.
Furthermore, the lack of ongoing monitoring prevents early detection of suspicious activity. It is therefore crucial to implement effective logging and monitoring practices, along with appropriate tools, to ensure application security and mitigate the risks associated with cyberattacks.

