A crucial element for the Red Team’s task is having stealth to perform the attack, success in the ability to expose an aggressive mindset and a true cracker’s point of view. If the red team wins, they can help building a better defense for the Blue Team in the future. This content on Firefox tunnel to bypass any firewall is meant for good purposes, don’t worry.
At this blog post, the content is about a different attack approach to get remote control of the machine and bypass the firewall. We have a lot of weapons to work in that perspective, something like veil framework, msfvenom… but sometimes following a different path, will generally bring good results.
The objective of the attack is to use Firefox to make all communication between client and server using hookings. This is not impossible, yet DLL injection sometimes can be boring to implement and even harder to make it portable. Did you know that x32 and x64 architecture need different approaches for development? (later I discovered that easyhook api can solve that).
I was studying the firefox internals, reading something about the use of SQLite to work with cookies, and that gave me a different focus.
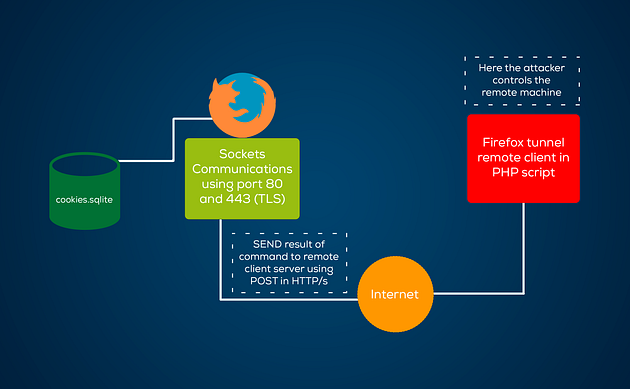
Look at the following image:

To create a program like firefox tunnel, follow these steps to get started:
- The program calls Firefox Browser in hidden mode, sends a URL that contains an evil server and finally that evil server sends a cookie with a command.
- Tunnel gets the cookie from evil server (cookie.sqlite) and uses that to call a command shell.
- The result of the command shell is used to write a HTML with javascript that auto submits the content result.
- The Program then opens a HTML in hidden mode and sends the result of CMD to the evil server.
Take a look:
In order to see this in action I have created a repository with everything you need and even a PoC.
In order to see this in action I have created a repository with everything you need and even a PoC.
Read also: Android pre-tests: Basic concepts and an introduction to the topic
Future insights:
- Insert persistence, using function RegOpenKeyEx() to open path “SoftwareMicrosoftWindowsCurrentVersionRun” and write with function RegSetValueEx() to launch a program automatically at system startup.
- Use images in I/O using steganography.
- Running process in hidden mode.
- Turn tunnel into an unkillable process.
Possible mitigations:
- Global hooking, to get OpenFile(), CreateFIle() functions and filter argv “cookie.sqlite” and block when programm route is different of firefox.exe.
- File watch api to monitor the database of cookies.
- Programm to open database of cookies by periodicity and search evil domain or hosts using query SELECT, that can use black list and uses DELETE query to remove the evil cookie.
- Consult us for more ideas.
Thank you Nash Leon for introducing me to headless trick.

1 Comment